Entropy
These are the visual aids I used to deliver a talk on font metric–based fingerprinting on January 26, 2015 at Financial Cryptography and Data Security 2015.
For the full paper see: https://www.bamsoftware.com/papers/fontfp.pdf.
University of
California, BerkeleyDavid Fifield,
University of
California, Berkeley
International Computer
Science InstituteSerge Egelman
Tracking you after you delete your cookies.
Tracking you after you change your IP address.
Uses measurements such as the User-Agent string, screen size, time zone, fonts, browser plugins—even things like CPU architecture and graphics card.
Try these:
https://panopticlick.eff.org/
https://amiunique.org/
Mainstream browsers don’t defend against even well-known attacks.
| Æ | Æ | Æ | Æ | Æ | Æ |
| default | serif | sans-serif | monospace | cursive | fantasy |
| (CSS generic font families) | |||||
|
→ |
|
|
|
→ |
|
||
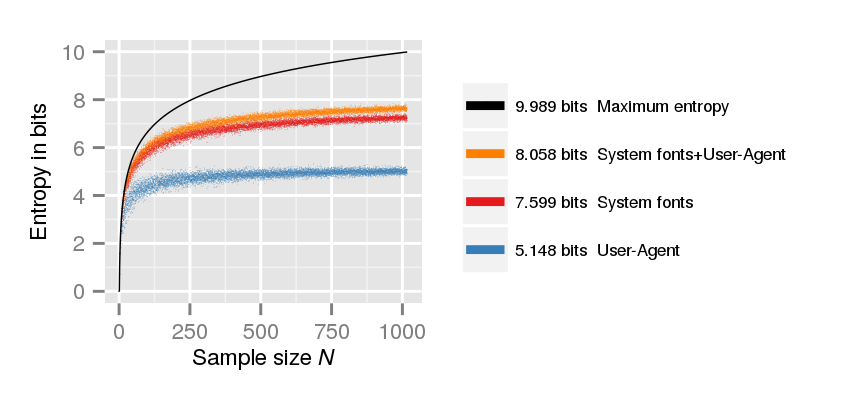
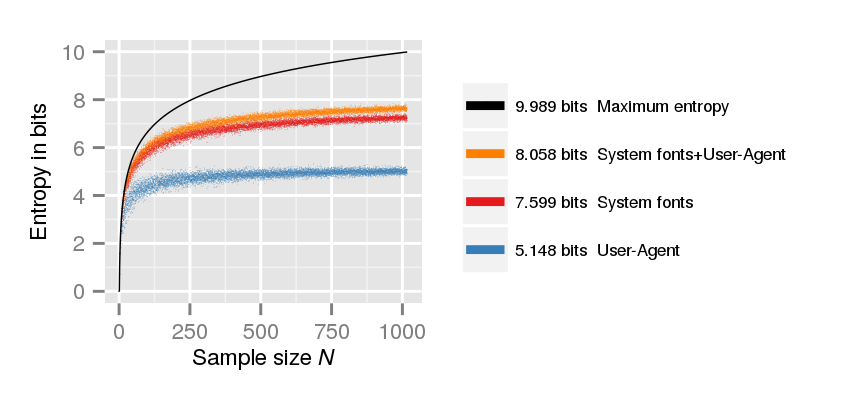
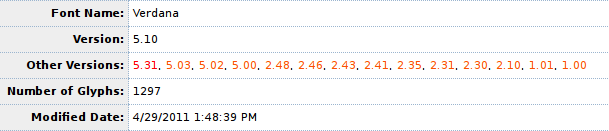
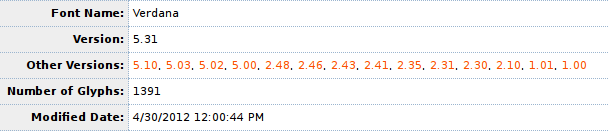
1,016 Mechanical Turk users.
(Max. possible entropy = 9.99 bits.)
User-Agent gives 5.15 bits; 175 distinct; 11% unique.
Font metric fingerprinting gives 7.60 bits; 444 distinct; 34% unique.
User-Agent plus font metrics gives 8.06 bits; 531 distinct; 43% unique.
| ☃ |
| U+2603 |
|---|
| ☃ | ⛄ | ⛇ |
| U+2603 | U+26C4 | U+26C7 |
|---|
| bi-directional | noncharacters |
| combining characters | unassigned code points |
| private use | … |
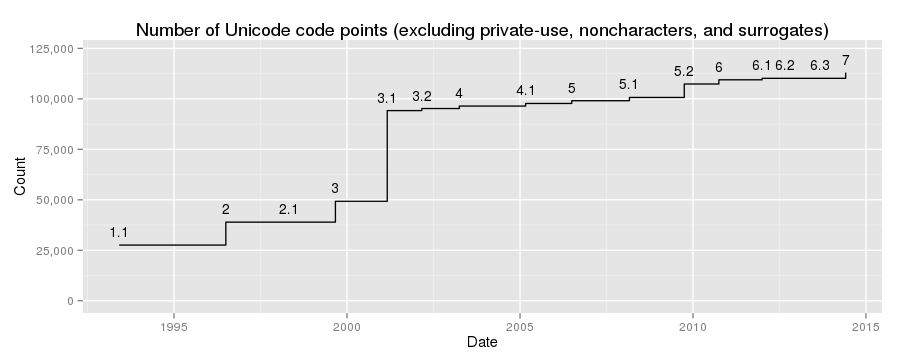
125,776 code points, whittled down to 43.
|
|
|
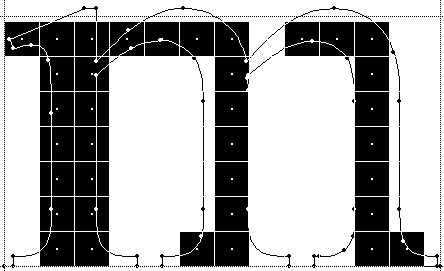
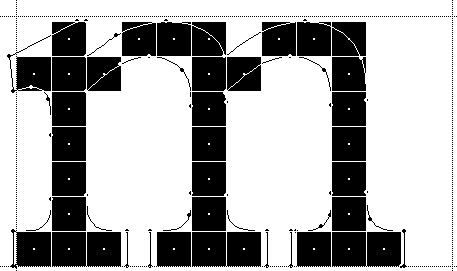
hinting/antialiasing
|
hardware rendering
|
|
|
https://www.microsoft.com/typography/tools/trtalr.aspx
http://www.rastertragedy.com/
 ≠
≠ 
 ≠
≠ 
Ship standard fonts with the browser, and use no fonts but those (i.e., don’t snarf random system fonts).
Normalize rendering settings (hinting, antialiasing, etc.) as much as possible.
Requires sensitivity to the needs of many writing systems.
Work in progress at https://bugs.torproject.org/13313.
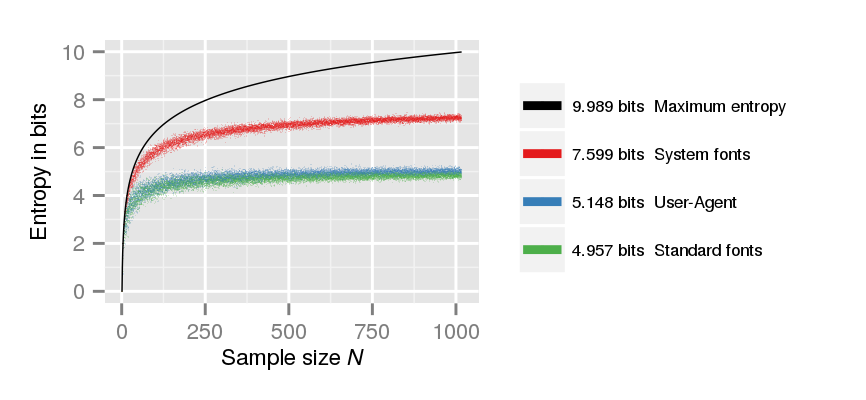
In the same Mechanical Turk experiment, we simulated the defense of using only browser-supplied fonts (by using standardized webfonts). The entropy due to font metrics dropped from 7.60 bits to 4.96 bits, lower than User-Agent.
Device fingerprinting is not insurmountable—but it’s a question of tradeoffs. (Recall CSS history sniffing.)
Fingerprinters have to work harder for worse results—that’s good!
fifield@eecs.berkeley.edu
git clone https://repo.eecs.berkeley.edu/git-anon/users/fifield/fontfp.git
https://www.bamsoftware.com/papers/fontfp.pdf
😁